Cybersecurity Fundamentals Bootcamp by Lexford International University
- Learn Ethical Hacking from Scratch
- Understand Network & Cloud Security
- No Prior Security Experience Required
- Master Vulnerability Scanning Tools
- Detect Malware & Phishing Attacks
- Mentorship from Senior Security Experts
- Hands-on Labs & Real-World Scenarios
- Prepare for Industry Certifications (CompTIA)
- Global Certification by Lexford University
- Access to top Information Security jobs

- Intro to Security
- Tech Landscape
- Program Highlights
- Why HNtrix
- Benefits
- Application
- FAQ
Cybersecurity Fundamentals
Learn to protect networks, systems, and data from digital attacks.
The Cybersecurity Fundamentals Bootcamp is a comprehensive, hands-on program designed to take you from a beginner to a knowledgeable security professional. This program covers the foundational principles of information security, ethical hacking, and network defense. You will learn essential concepts such as identifying vulnerabilities, understanding malware and phishing, cryptography, and securing cloud environments. We also cover practical tools used by professionals to monitor networks and defend against cyber threats. Participants will work on real-world scenarios, setting up secure environments, analyzing risk, and managing security protocols, providing the practical experience needed to excel in modern IT security roles.
Why Choose Cyber Security ?
Security is the highest priority for every modern digital enterprise.
Growth in open cybersecurity positions over the last 5 years, outpacing other IT fields.
Cybersecurity has had a 0% unemployment rate for over a decade globally.
Estimated global shortage of cybersecurity professionals by the end of 2025.
The average base salary for Information Security Analysts in top global markets.
Cyber defense is recognized as a mission-critical skill for organizations worldwide.
Upon completion of the Cybersecurity program, students will:
- Understand and identify common vulnerabilities in networks, web applications, and operating systems.
- Perform basic penetration testing and ethical hacking using industry-standard tools like Nmap and Metasploit.
- Analyze and defend against social engineering attacks, phishing, and common malware variants.
- Implement basic security protocols, encryption methods, and robust identity access management (IAM).
- Develop the foundational knowledge required to pursue entry-level roles such as Security Analyst or SOC Analyst.

Program Highlights
See which benefits you can derive from joining this program.
Foundational Security
- Learn core IT and networking basics first.
- Understand the CIA Triad (Confidentiality, Integrity, Availability).
- Highly Experienced Security Instructors.
Ethical Hacking Basics
- Introduction to Kali Linux and command-line tools.
- Learn the methodology of Penetration Testing.
Live Mentorship & Support
- Weekly Live Threat Analysis Sessions
- 1-on-1 lab troubleshooting & project guidance
- Dedicated Tech Support to help with virtual environments.
Become Job-Ready
- Build a strong portfolio with practical security labs.
- Curriculum aligns with CompTIA Security+ principles.
- Learn industry best practices for defense in depth.
Program Curriculum
An overview of what you will learn from this program.
- Understand the foundation of the internet. Learn about IP addresses, DNS, TCP/IP models, routing, and how data moves securely across networks.
- Dive into the core of security. Understand the CIA triad, risk management, threat modeling, and the psychology behind social engineering and phishing attacks.
- Learn the phases of a cyber attack (Reconnaissance, Scanning, Gaining Access, Maintaining Access). Get hands-on with basic Kali Linux commands.
- Use industry-standard tools like Nmap and Nessus to scan networks, discover open ports, and identify potential software vulnerabilities before hackers do.
- Learn how to control who has access to what. Explore password policies, multi-factor authentication (MFA), and Role-Based Access Control (RBAC).
- Understand how data is kept secret. Learn the difference between hashing, symmetric encryption, and asymmetric encryption (PKI), and how digital certificates work.
- Learn what to do when a breach happens. Understand the basics of firewalls, Intrusion Detection Systems (IDS), and how a Security Operations Center (SOC) operates.
- Apply your knowledge in a simulated environment. Perform a vulnerability assessment on a mock network and write a professional security report detailing your findings.
Capstone Projects
Test your security skills with practical lab simulations.
Network Vulnerability Scan
Use Nmap and Wireshark to map a simulated network, discover open ports, and document potential attack vectors.
Phishing Campaign Simulation
Design and execute a safe phishing simulation to test employee awareness and analyze the click-rate data.
Password Cracking Lab
Learn how weak passwords are exploited by running a dictionary attack against hashed passwords in a controlled lab.
Malware Analysis
Safely isolate and analyze a basic malware sample in a sandbox environment to understand its behavior and indicators.
Firewall Configuration
Write and test access control list (ACL) rules for a virtual firewall to block malicious IPs while allowing valid traffic.
Security Audit Report
Compile a professional vulnerability assessment report detailing risks, impacts, and remediation strategies.
Social Engineering Analysis
Techniques used: OSINT (Open Source Intelligence) gathering to profile a mock target for potential physical security risks.
Data Encryption Implementation
Techniques used: Apply AES and RSA encryption tools to securely transmit files across a simulated corporate network.
Why HNtrix
Enrol with leading global online educational Security course provider.
Cybersecurity Batch Profile
Experience Distribution
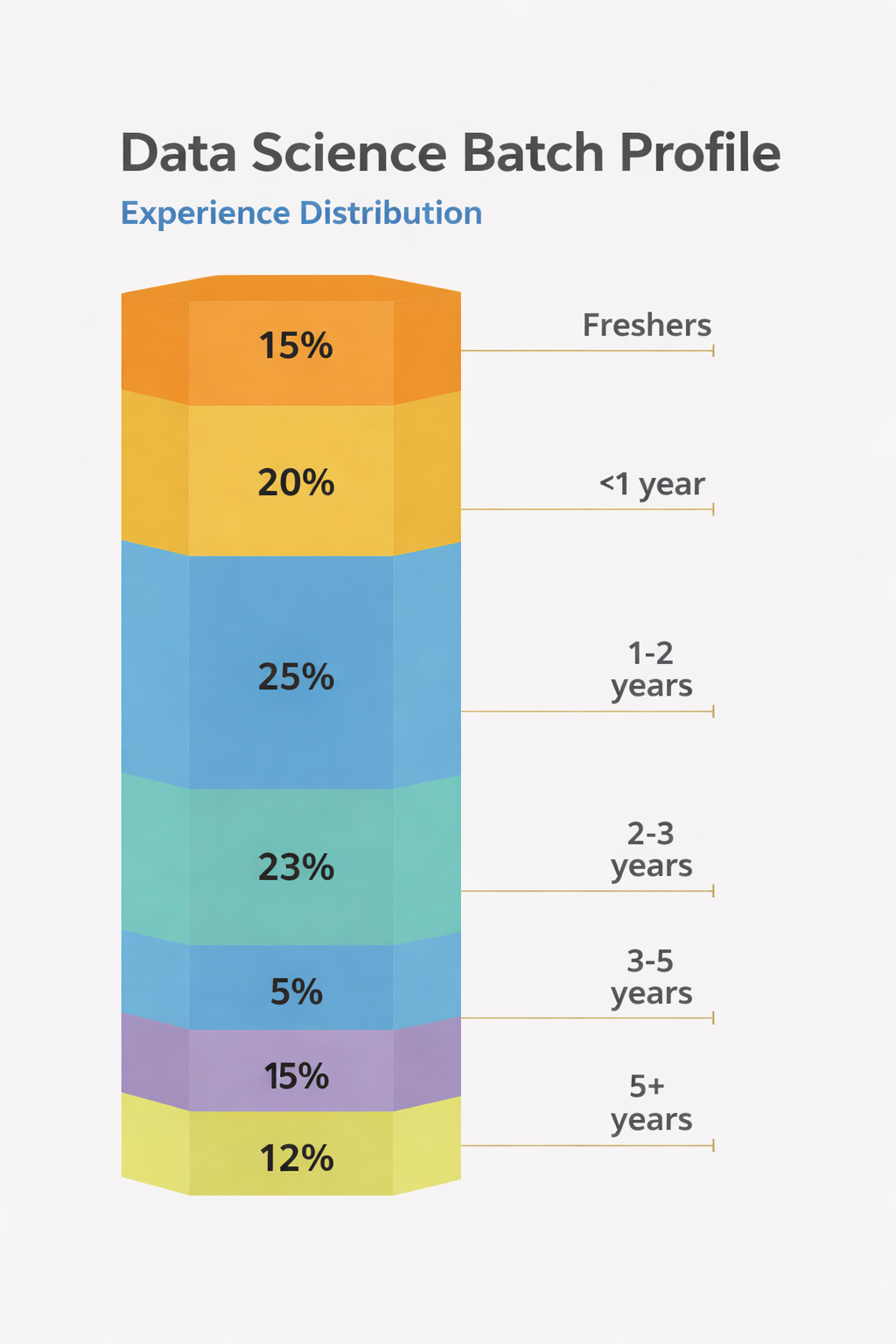
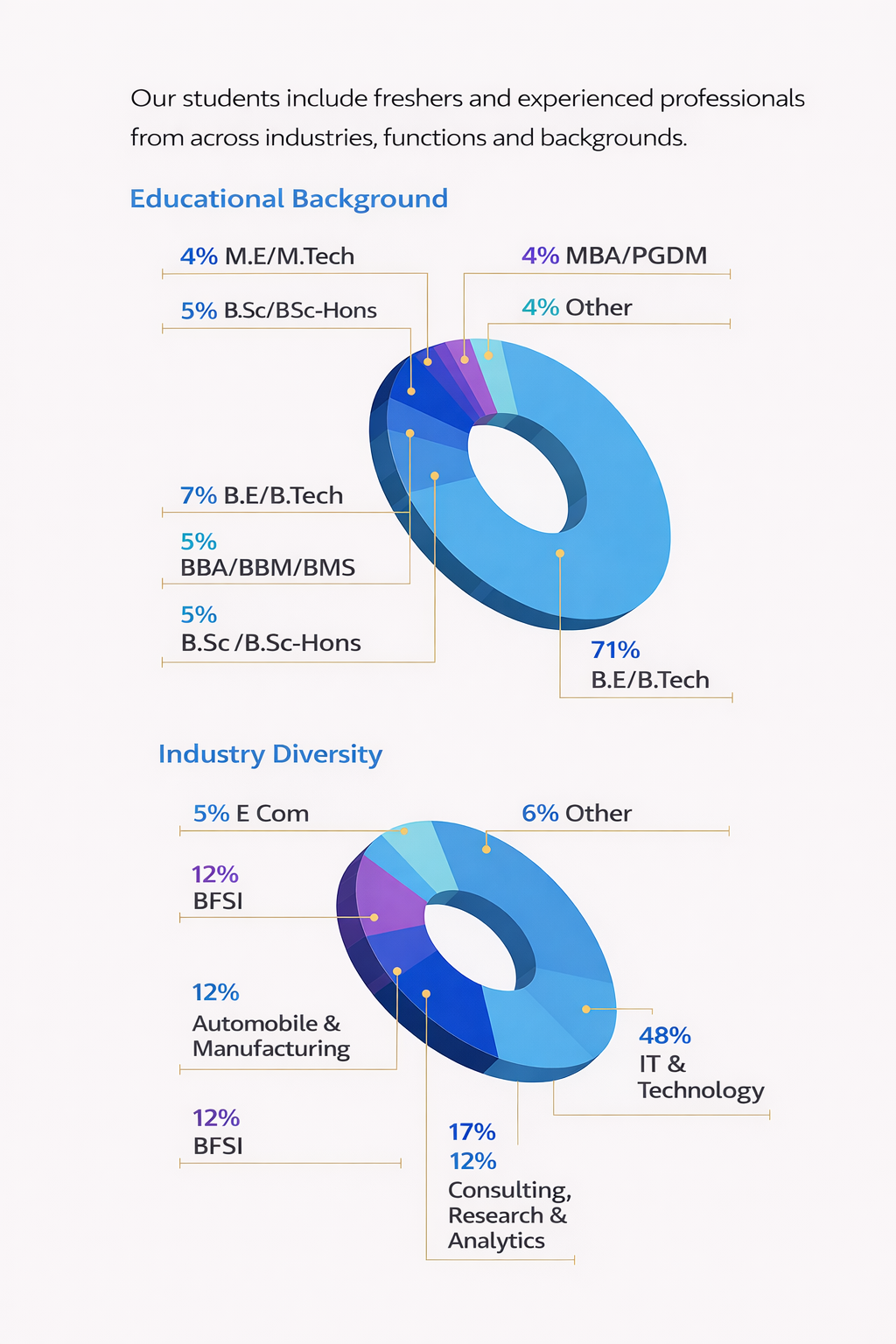
Our students include fresh IT graduates, network administrators, and non-tech professionals looking to build a career in Information Security.
Benefits
Learn Security from leading academicians and experienced practitioners.
Personalised security labs based on your proficiency level to give you hands-on experience.
Mix of Live Concept Classes & Recorded lab walkthroughs for your convenience.
24*7 Student Support, Quick vulnerability debugging by industry experts
Alumni Highlights
- 200+ Global Companies
- $105K PA Average CTC
- $210K PA Highest CTC
- 88% Career Transition Rate
Security Roles
Offered
Trusted By Learners Across Top Companies
We Have Users For Our Security Program From Following Companies





























Application Process
Enroll in the Cybersecurity program with a simple online form.
Apply by filling a simple online application form
Admissions committee will review your IT goals.
Shortlisted candidates join an introductory call.
Screening call with Alumni/ Faculty and confirmation.
FAQ
Find answers to all your queries and doubts here.